Cyber threats are becoming more common, not only in the business scene, but also at home. Cyber risks include online extortion & ransomware, cyber bullying, identity theft, system compromise, data breach, reputation damage and more. With technology changing daily, your risk changes - so here's what you need to know to help mitigate (insurance speak for minimize) your risk as much as possible.

Technology is great, right? Kindof...
70% Of all personal devices are susceptible to a hack right now. How many of you have posted food pix while out for dinner? Family vacation pictures? All it takes is for your Facebook, Twitter, Instagram, and even TikTok account to be viewed by the wrong person. Suddenly your fresh seafood plate in Cancun is a criminal's "go ahead" to ransack your home. Or your innocent "Hamilton was fantastic in Chicago this evening!! #loveHamilton! - at the CIBC Theatre" post lets the hackers know they have a day or so to get the info they need. Even Fitbits are being hacked to access sleeping patterns and home arrival times to increase the advantage of a successful burglary!
 Fear the pineapple!
Fear the pineapple!
"Pineapple" is a tech term for those common areas you visit (ex: hotels, restaurants, schools, malls, sporting events) where a hacker can use a common name for their network device, related to the area in which you are visiting. For example, if you are visiting a Hinckley Knights baseball game, there may be a Wi-Fi network that pops up named "WinKnights." Without hesitation, you assume this is their secured network, and you connect
Free Wi-Fi, right?
Wrong. Now that hacker can download an app into your phone, without you even knowing it. Monday morning, you go into work and charge your phone through the USB port in your work computer. The hacker now has a freeway to your work computer, along with full access to infiltrate your business systems. Even "secure" Wi-Fi networks can gain information about you - which is NOT illegal at this time. Yikes!
Advanced Persistent Threats (APTs)
With "advanced persistent threats" and hacking in general - it's not all about credit card fraud anymore. Personal information, intellectual property, designs, and more can be sold for a price on the dark web. Getting an email from someone or some company you do not know should throw red flags, especially those with attachments or links. Attachments could be a segway for a breach. Some hackers even download seeing or sound programs onto your device without you even knowing, allowing them to see and listen to what you are doing. The majority of APTs have an attachment or link you must click for a Cyber Threat to happen.
We've seen where the virus gets on the device, and it "appears" to be warning the user there is a virus. And for a small fee (of hundreds of dollars) the virus will fix itself. Classic cyber threat! Do. Not. Click. Do. Not. Pay.
 So what can you do?
So what can you do?
While knowledge is key, it's nearly impossible to know about every type of threat out there. What you can do is be cautious.
- Don't "post" when you are away from your home - on vacation, out of town, etc.
- Don't share standard routines - you are always at your cabin and away from your home each weekend in the summer
- Be cautious about the "free Wi-Fi" networks you connect to
- Do not open emails from unknown sources. Hint: While it may appear to be from "Apple" or "Netflix" - a quick mouse-hover over the from-field in the email will identify the real email address it is coming from. Use your judgement to gauge if it is legit or not. Err on the side of caution!
- Never click links to update your account settings such as verifying your payment information.
- Do not open attachments from unknown senders, on home and work computers.
- Search or Google "free anti-virus" and "anti-malware software." There are many well-known, free programs - such as Avast, AVG, Microsoft Windows Defender and Malwarebytes. These programs are good to have on your computer BEFORE you get attacked.
- Contact your local computer repair business, they will share some of their insights and suggestions to help you be proactive as well!
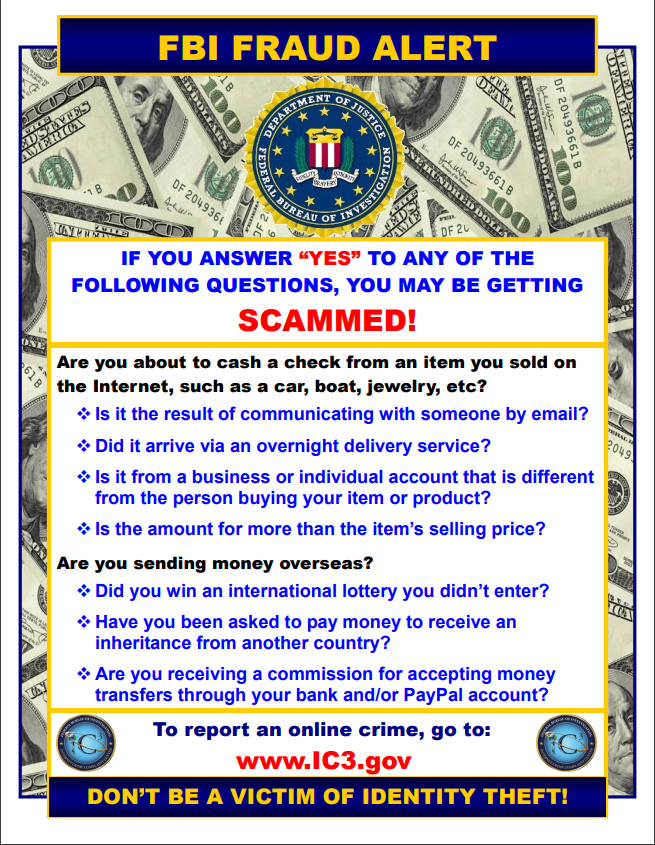
- Report any suspicious or fraudulent looking activities through the Internet Crime Complaint Center (IC3).
What are we doing for you?
Some homeowners insurance policies are now offering Cyber Coverage. Contact your agent to see if your current carrier offers this endorsement. This endorsement may cover:
- Online Extortion - Expenses and ransom paid for threats to cause a network disruption;
- Cyber Bullying Response - Costs for counseling, tutoring, temporary relocation, tuition expense;
- Identity Theft - Cost and help in reclaiming your policyholder's identity;
- System Compromise - Data recovery and system restoration needs;
- Internet Clean-Up - Expenses associated with removing false statements on the internet;
- Breach Cost - Costs associated with notification, investigation, and monitoring a breach.
For businesses, Cyber Breach Coverage has been around for a handful of years. If you have a Cyber policy, I urge you to review the limits and coverage. Some carriers that offer cyber don't give enough initially, or coverage is limited. With possible fines from the state, coverage and limits may not even come close to covering a major unexpected hit to your bottom line.
While certainly technology can be a great tool for home and work, we do need to be mindful of where, what and when we are using social media, accessing servers, and opening emails. The threat is becoming more and more common.
Written by Gabe Cessna, commercial lines agent in the Hinckley office, with data provided by Ram Mutual Insurance and EMC Insurance Company.

 Fear the pineapple!
Fear the pineapple! So what can you do?
So what can you do?